-
-
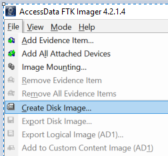
Create Forensic Image
-
Step-by-Step Guide to Creating a Forensic Image with FTK Imager
While many computer forensic software manufacturers create excellent tools, most require the purchase of a software license. Years ago, the software manufacturer Access Data took a leap and released a completely free tool for forensic image creation tool, which is called FTK Imager and can be obtained from their website - www.accessdata.com. It became a standard for whole disk forensic imaging. Forensics professional can create a forensic image of a wide number of devices, such as local hard drives floppy diskette(s), zip disk(s), cd/dvd(s), individual file(s) or entire folder(s). This forensic image is a bit-by-bit copy of the identified data. The forensic examiner can place this data into different forensic image formats to include the Expert Witness format by Encase (e01), Smart, AFF or a raw dd format. Once the forensic image is created, forensics professional can preview the contents of the newly created forensic image. This lets the user understand what type of data is available within the image. The deleted data will also be displayed to the extent that it is available. This image can also be mounted as read-only and allows the data to be examined in a format similar to Windows Explorer. Once critical files/folders are identified, this information can be exported from the forensic image onto the user's system. For example, if the user is looking for a particular document, this data can be extracted and opened by the native application. Additionally, a hash value can be created for this file. A hash value is the equivalent of the digital Let's assume a hard drive needs to have a computer forensic examination. The first step is to secure the system. Once the system is secured, power it off and remove the system's hard drive. The hard drive should be connected to a write blocker and then connected to a imaging system. Once the system is powered on - launch FTK Imager by double clicking the icon. Select File - Create Disc Image.
|

 fingerprint. The two most commonly used by computer forensic professionals are MD5 (Message Digest 5) and SHA (Secure Hashing Algorithm).
fingerprint. The two most commonly used by computer forensic professionals are MD5 (Message Digest 5) and SHA (Secure Hashing Algorithm).